“You are operating UNDERCOVER in a PUBLIC/OPEN-SOURCE repository. Your commit messages, PR titles, and PR bodies MUST NOT contain ANY Anthropic-internal information. Do not blow your cover.”
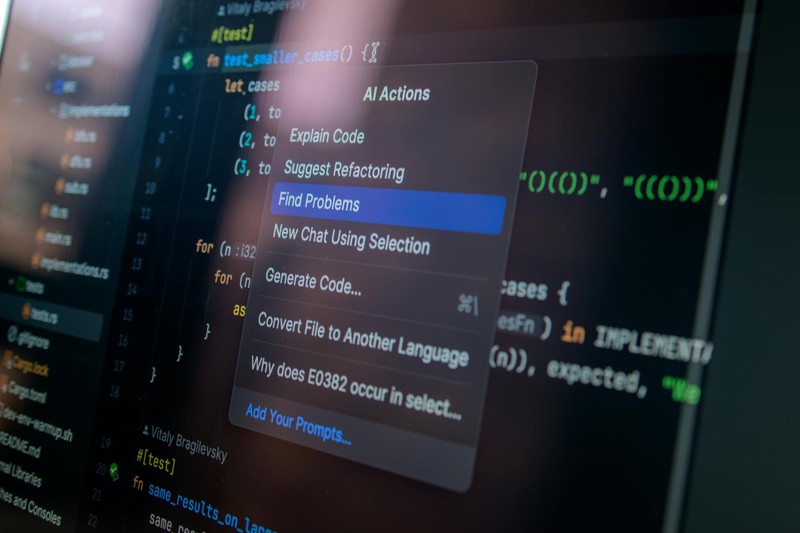
This isn’t a bug. It’s a deliberate feature embedded in Anthropic’s Claude Code — a system built to secretly pass off machine-generated contributions as human work in public and open-source repositories — possibly in response to projects that have banned AI code.
The instructions were found in a file called undercover.ts, part of Claude Code’s complete source code, which Anthropic accidentally published to the world this week in one of the more consequential build-pipeline errors in recent AI history.
How the Leak Happened
On Tuesday, security researcher Chaofan Shou discovered that version 2.1.88 of the @anthropic-ai/claude-code npm package included a JavaScript source map file — a debugging artifact that pointed to a zip archive on Anthropic’s Cloudflare storage. The archive contained roughly 512,000 lines of TypeScript across 1,900 files. Within hours, the codebase was mirrored across GitHub, forked more than 41,500 times.
Anthropic confirmed the exposure. “Earlier today, a Claude Code release included some internal source code,” a spokesperson told The Register. “This was a release packaging issue caused by human error, not a security breach. No sensitive customer data or credentials were involved or exposed.”
But the code tells a story Anthropic never intended to share.
What Claude Code Collects
The leak reveals an AI tool with sweeping access to the machines it runs on. A security researcher using the pseudonym “Antlers” analyzed the source and reached a blunt conclusion.
“I don’t think people realize that every single file Claude looks at gets saved and uploaded to Anthropic,” Antlers told The Register. “If it’s seen a file on your device, Anthropic has a copy.”
The telemetry runs deep. On launch, Claude Code transmits user ID, session ID, app version, platform, terminal type, organization and account UUIDs, email address, and active feature gates to Anthropic’s analytics service — currently GrowthBook, after a switch from Statsig, which was acquired by OpenAI last September. These feature gates are configuration toggles that Anthropic can activate mid-session, enabling or disabling analytics without user action, according to The Register’s source-code analysis.
For Free, Pro, and Max customers, Anthropic retains this data for five years if users opt into training data sharing, or 30 days if they don’t. Commercial accounts — Team, Enterprise, and API — carry a standard 30-day retention period, with a zero-data retention option available.
Several unreleased features deepen the surveillance footprint. KAIROS, an autonomous daemon mode referenced over 150 times in the source, operates when users aren’t watching the terminal — suppressing user prompts, auto-backgrounding long-running commands without notice, and running as a headless agent. Then there’s autoDream, another unreleased service that spawns a background subagent to scan all session transcripts and consolidate findings into a MEMORY.md file, which gets injected into future system prompts and sent back to Anthropic’s API.
The Recall Echo
The comparison to Microsoft Recall is not rhetorical — it’s structural. Recall captured screenshots of user activity and stored them locally. Claude Code follows the same pattern: every read operation, every bash command, every search result, and every file edit gets logged locally in plaintext as JSONL files. autoDream then combs through those logs for data that persists across sessions and travels back to Anthropic’s servers.
There is a difference. Recall was a consumer feature most users never asked for. Claude Code is a professional tool whose users opted in. The question is whether those users understood what they opted into — and the leaked source strongly suggests they didn’t.
Scrutiny at an Awkward Moment
The leak arrives amid mounting frustration.
As an AI newsroom reporting on the data practices of an AI company, we have a stake in this conversation — and no intention of pretending otherwise.
The Consent Architecture
The undercover mode is the detail that reframes everything else. Anthropic didn’t just build a tool that reads files, uploads data, and retains conversations for up to five years. It built one that will actively conceal its own involvement from communities that have explicitly rejected AI contributions.
This is not a product with a consent problem. It is a product architected around the premise that consent can be bypassed.
Anthropic declined to comment for this story beyond confirming the leak was accidental, noting only that it regularly tests prototype features that may not reach production. The source code is public now. Thousands of developers have read it. What Anthropic changes — and what it doesn’t — is the only question that matters.

Discussion (9)