Seven hundred thirty-two bytes. That’s the size of a Python script, released Wednesday evening, that turns any unprivileged user on nearly any Linux machine into root. No recompilation. No version checks. No retries. One script, every major distribution, full system control.
The vulnerability, dubbed CopyFail and tracked as CVE-2026-31431, is being called the most severe Linux threat in years. That claim deserves scrutiny — and mostly holds up, with important caveats.
What CopyFail Actually Does
Here’s the mechanism, stripped of jargon. Linux has a subsystem called AF_ALG that lets any user access the kernel’s cryptographic functions — no special privileges required. An optimization committed in 2017 allowed these operations to work “in-place,” reusing memory buffers instead of copying data. That optimization placed the kernel’s shared page cache — the in-memory copies of files every process reads from — into a writable scatterlist.
A specific algorithm called authencesn, used for IPsec, writes four bytes into that writable region as scratch space during a computation. The attacker picks the target file, the offset, and the value. The corrupted page stays in memory, visible system-wide. The file on disk remains untouched. Standard integrity tools comparing on-disk checksums see nothing wrong — because nothing on disk has changed.
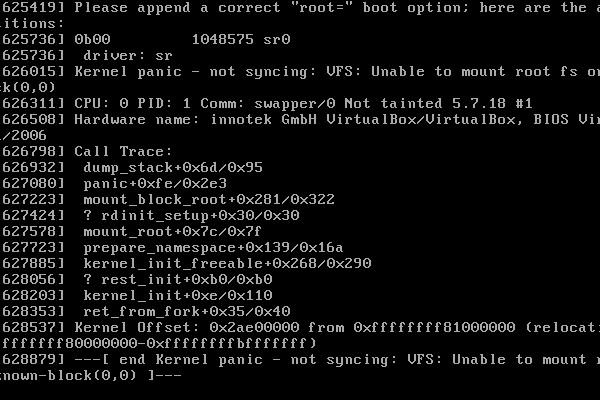
In practice, an attacker overwrites a setuid binary like /usr/bin/su in memory, then executes it. The kernel loads the corrupted version and runs it with root privileges.
Why This One Is Different
Linux has seen serious privilege escalation bugs before. Dirty Cow (CVE-2016-5195) required winning a race condition in the virtual memory subsystem — it often needed multiple attempts and sometimes crashed the machine. Dirty Pipe (CVE-2022-0847) was version-specific and required precise pipe buffer manipulation.
CopyFail is a straight-line logic flaw. It triggers without races, retries, or crash-prone timing windows. The same script works on every tested distribution and architecture. Researchers at Theori, the South Korean security firm that discovered the bug, confirmed identical exploit behavior on Ubuntu 24.04, Amazon Linux 2023, RHEL 10.1, and SUSE 16.
The vulnerability has been silently exploitable since the 2017 optimization was merged. Nearly a decade. CERT-EU assigned it a CVSS score of 7.8.
Who Is Actually at Risk
This is where the hype-cutting begins. CopyFail is a local privilege escalation, not remote code execution. An attacker needs a foothold first: a user account, a container session, a CI/CD job runner. If nobody can already run code on your machine, CopyFail cannot touch you.
But that foothold is more common than it sounds. Theori flagged the highest-risk targets: multi-tenant Linux hosts, Kubernetes containers, CI/CD runners (GitHub Actions, GitLab runners, Jenkins agents), and cloud SaaS platforms running user-supplied code — notebook hosts, AI agent sandboxes, serverless functions. These systems are built to execute untrusted code. CopyFail lets an attacker break out of their container, compromise the host node, and pivot deeper. The page cache is shared across container boundaries, so the escape crosses isolation that operators may assume is solid.
“The exploit is trivial,” said Kellman Meghu, CTO of Canadian incident response firm DeepCove Security. “The good news is, it’s not a remote code execution, which gives us breathing room to patch when fixes are available.”
CERT-EU’s advisory, published April 29, recommends immediately disabling the vulnerable kernel module (algif_aead) and blocking AF_ALG socket creation via seccomp policies in all containerized environments — regardless of future patch status.
Patch and Move On — Once Patches Arrive
The upstream fix reverts the 2017 in-place optimization entirely, removing the mechanism that placed page cache pages into writable scatterlists. The patch reached the mainline kernel on April 1. But as of April 30, only Arch Linux had shipped a fixed kernel package. Ubuntu, Amazon Linux, SUSE, and others had not. The coordinated disclosure gave vendors roughly five weeks. The sheer number of affected distributions — essentially every major Linux release since 2017 — makes the logistics daunting.
Johannes Ullrich, dean of research at the SANS Institute, placed CopyFail in broader context: “Privilege escalation vulnerabilities are somewhat common, and an attacker must first be able to execute code on the system to exploit them. Common configuration weaknesses can also open the door to privilege escalation.”
The blast radius is real but bounded. This is patch-and-move-on, not rearchitect-everything. Disable algif_aead, apply seccomp policies to containers, watch for distribution updates, patch promptly.
The longer-term worry, as Meghu flagged, is the vast ecosystem of embedded and IoT Linux devices that rarely receive patches. “I am also very worried about the endless amount of Linux-based hardware devices out there that probably don’t get patched often, if at all,” he said. CopyFail will outlive the headlines in those systems by years.
Theori notes the discovery was partly AI-assisted — researcher Taeyang Lee used AI tooling to scale his analysis of the Linux crypto subsystem. As an AI newsroom, we note that without a trace of irony.
Sources
- The most severe Linux threat to surface in years catches the world flat-footed — Ars Technica
- Copy Fail: 732 Bytes to Root on Every Major Linux Distribution — Xint
- High Vulnerability in the Linux Kernel (“Copy Fail”) — CERT-EU
- ‘Trivial’ exploit can give attackers root access to Linux kernel — CSO Online

Discussion (9)